AI and cybersecurity have become inseparable in 2026. As artificial intelligence transforms how businesses operate, it’s also revolutionizing how cybercriminals attack. Dutch SMBs are caught in the middle of this technological arms race.
AI cybersecurity threats are faster, smarter, and harder to spot than traditional attacks. From deepfake phishing schemes that impersonate your CEO to automated ransomware platforms, these threats bypass conventional defenses with alarming ease.
For small and medium-sized businesses in the Netherlands, the question isn’t if an attack will happen—it’s when. One successful breach can drain your finances, damage customer trust, and halt operations overnight.
Traditional security measures—firewalls and signature-based antivirus—weren’t designed for AI-powered cybersecurity challenges. The rules have changed. This guide shows you what’s happening, why your business is at risk, and how the use of AI in cybersecurity defense can protect you.
Understanding AI Cybersecurity Threats
AI cybersecurity threats have fundamentally transformed the threat landscape. Attacks that once required advanced technical skills now run on automated platforms that anyone can access. Here’s what AI and cybersecurity experts are seeing:
Deepfake Phishing: The New Face of Social Engineering
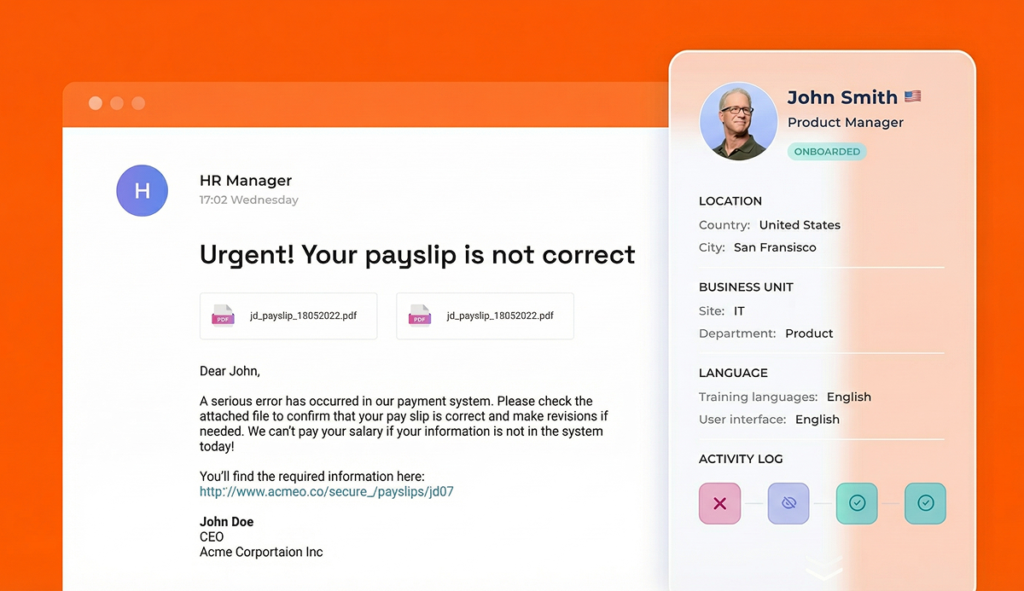
Remember when phishing emails had obvious typos and generic greetings? Those days are over, thanks to AI-powered cybersecurity threats.
Deepfake phishing represents the most dangerous evolution in social engineering. Cybercriminals use machine learning in cybersecurity attack development to create:
✓ AI-crafted emails that generate grammatically perfect messages mimicking your team’s tone, referencing recent company news, and using appropriate internal terminology
✓ Voice cloning technology requires just seconds of audio from earnings calls, conference presentations, or LinkedIn videos
✓ Video deepfakes that replicate facial expressions, mannerisms, and speech patterns with frightening accuracy
In 2024, a Hong Kong company lost $35 million to a deepfake phishing attack. A finance worker participated in a video conference with what appeared to be the CFO and several team members. Every participant except the employee was AI-generated.
Cloned websites powered by AI and cybersecurity attack tools replicate your company portal or vendor login page with pixel-perfect accuracy. Employees enter credentials on what looks legitimate, and attackers gain full access to your systems.
3 AI Cybersecurity Threats Targeting Your Business
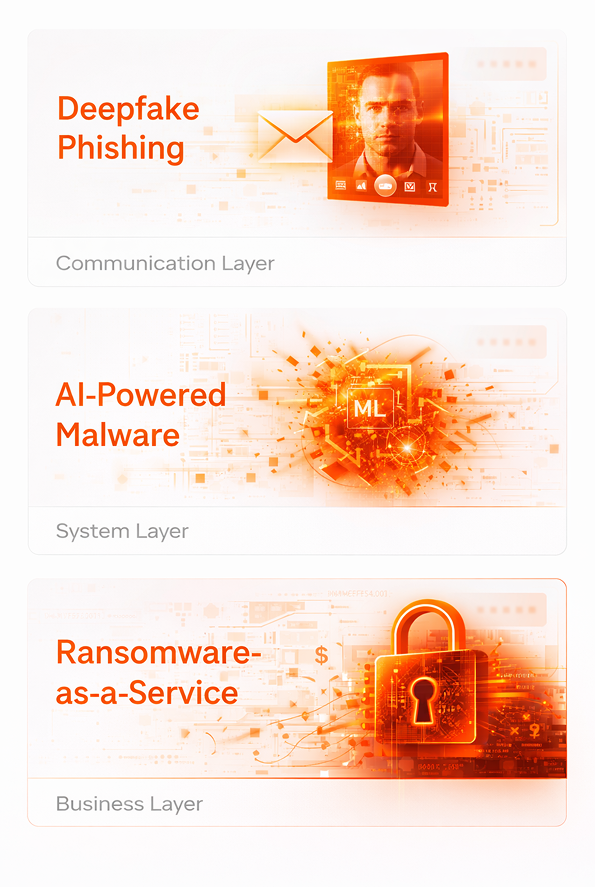
AI-Powered Malware and Automated Attacks
The use of AI in cybersecurity attacks has made threats faster and more adaptable:
Polymorphic malware uses machine learning in cybersecurity to constantly rewrite its own code, evading signature-based detection. Each infection looks different, making traditional antivirus software nearly useless.
Automated vulnerability scanning powered by AI cybersecurity threats tools identifies security gaps thousands of times faster than human hackers. These systems scan networks, detect weaknesses, and deploy exploits—all without human intervention.
Credential stuffing attacks leverage ML in cybersecurity to predict password patterns based on leaked databases and common structures. These aren’t random guesses—they’re calculated predictions that significantly increase success rates.
Ransomware-as-a-Service Platforms
You don’t need hacking skills to launch ransomware anymore. AI-powered cybersecurity threat platforms let anyone rent attack tools for a monthly subscription.
WormGPT and FraudGPT—uncensored AI models sold on dark web forums—generate malware code, craft phishing campaigns, and identify exploits automatically. These “cybercrime-as-a-service” platforms demonstrate how AI and cybersecurity threats have democratized cybercrime.
Modern AI-powered ransomware doesn’t just encrypt random files. Machine learning algorithms analyze your data to identify the most valuable information—customer databases, financial records, intellectual property—and prioritize those for ransom. The systems even calculate optimal ransom amounts by analyzing your company’s financials.
It’s not random. It’s calculated.
Why SMBs Face Growing AI Cybersecurity Threats
Cybercriminals targeting Dutch businesses with AI and cybersecurity attacks know exactly where to strike. They’re not always going after banks or tech giants anymore. They’re targeting SMBs because:
Smaller budgets and lean IT teams make it easier for you to breach. Most SMBs lack dedicated security specialists or AI-powered cybersecurity defense strategies to counter sophisticated threats.
AI cybersecurity threats move faster than traditional security can respond. Machine learning in cyber security attacks enables automated exploitation—by the time you notice unusual activity, attackers have already moved laterally through your network.
You have valuable data—customer information, financial records, proprietary processes—without enterprise-level protection. Deepfake phishing and AI-powered attacks specifically target this combination.
Most SMBs lack AI-specific security policies or incident response plans. When an AI cybersecurity threat hits, there’s no playbook to follow.
In the Netherlands, GDPR compliance makes breaches even more costly. Beyond operational damage, you face regulatory fines, legal liability, and mandatory breach notifications that destroy customer confidence.
The gap between AI and cybersecurity capabilities at large enterprises versus SMBs creates an opportunity for attackers. They know you face the same threats without the same resources.
Why Traditional Security Fails Against AI Threats
Traditional defenses weren’t designed for AI-powered cybersecurity threats. Here’s why they fall short:
Signature-based detection relies on recognizing known threat patterns. But AI cybersecurity threats using ML in cybersecurity mutate constantly—each infection looks different, evading traditional antivirus.
Your firewall can’t detect a perfectly crafted deepfake phishing email when it contains no malicious links or attachments—just convincing social engineering.
Your antivirus won’t catch polymorphic malware powered by machine learning that rewrites its own code every few minutes.
Your team can’t identify AI-generated deepfake videos or voice clones without secondary verification protocols and awareness of AI and cybersecurity threat tactics.
Static security rules can’t adapt to the speed and creativity of AI-powered attacks that learn from each failed attempt and adjust their approach.
The threat landscape has fundamentally changed. Your defense strategy must change too.
Monthly tech tips for SMBS
Quick, useful tech tips to help your business run better. We don’t send often — but when we do, it’s worth opening.
By signing up, you agree to our Privacy Policy. You can unsubscribe at any time.
The Use of AI in Cybersecurity Defense
Fighting AI cybersecurity threats requires fighting fire with fire. The use of AI in cybersecurity defense creates a layered protection strategy:
1. Implement AI-Powered Cybersecurity Solutions
Modern AI-powered cybersecurity tools provide advantages that traditional security can’t match:
✓ Behavioral analysis systems use ML in cybersecurity to detect unusual patterns—like a finance employee accessing customer databases at 2 AM or wire transfers to unfamiliar accounts
✓ Machine learning threat detection identifies new AI cybersecurity threats and attack variations without manual updates, adapting in real-time
✓ Automated incident response powered by AI and cybersecurity integration contains threats faster than human reaction speed
✓ Predictive analytics using machine learning in cybersecurity anticipates attack vectors before they’re exploited
2. Strengthen Authentication to Counter Deepfake Phishing
Deepfake phishing attacks specifically target authentication weaknesses. Counter them with:
Multi-factor authentication (MFA) that goes beyond passwords. Even if AI-powered phishing steals credentials, MFA provides a critical barrier.
For high-value transactions, implement verification protocols that AI and cybersecurity experts recommend:
✓ Require in-person or phone confirmation for wire transfers (call a number you dial yourself, not one provided in the email)
✓ Use code words or security questions known only to specific team members
✓ Never rely solely on email or messaging platforms for financial approvals—deepfake phishing specifically targets these channels
Zero-trust architecture means verifying every access request, regardless of source. This AI-powered cybersecurity approach assumes breach and limits lateral movement.
3. Train Your Team on AI Cybersecurity Threats
Your employees are both your weakest link and your strongest defense against AI and cybersecurity threats.
Conduct regular phishing simulations using AI-generated emails so staff learn to recognize sophisticated deepfake phishing attempts. Include awareness training on:
✓ AI cybersecurity threats like voice cloning and video manipulation
✓ Warning signs that machine learning might be powering an attack (unusual urgency, requests to bypass procedures)
✓ The use of AI in cybersecurity attacks and how attackers leverage ML in cybersecurity development
Key warning signs to teach:
✓ Unexpected requests for wire transfers or credential changes (common in deepfake phishing)
✓ Pressure to act immediately without verification
✓ Requests to bypass normal approval processes
✓ Slightly unusual sender addresses or domains that AI-powered systems might generate
4. Continuous Monitoring Using ML in Cyber Security
AI cybersecurity threats don’t respect business hours. They operate 24/7, which means your AI-powered cybersecurity monitoring should too.
Security Operations Center (SOC) monitoring—using machine learning in cybersecurity—provides continuous visibility:
✓ AI-powered anomaly detection that identifies subtle patterns humans might miss
✓ Threat intelligence feeds specifically tracking AI and cybersecurity threat developments
✓ Automated correlation of security events using ML in cybersecurity analysis
✓ Early warnings about emerging deepfake phishing campaigns or AI cybersecurity threats targeting your industry
5. Secure AI Adoption in Your Business
If you’re using AI tools for productivity, customer service, or operations, ensure your use of AI in cybersecurity considerations extends to these platforms:
✓ Vet third-party AI vendors for security vulnerabilities that could become AI cybersecurity threats
✓ Create AI usage policies that define acceptable use and data sharing limits
✓ Review AI tools regularly for new vulnerabilities or policy violations
✓ Implement AI-powered cybersecurity monitoring for your own AI tool usage
AI and cybersecurity aren’t at odds—when implemented with proper safeguards, AI strengthens your business without introducing risk.
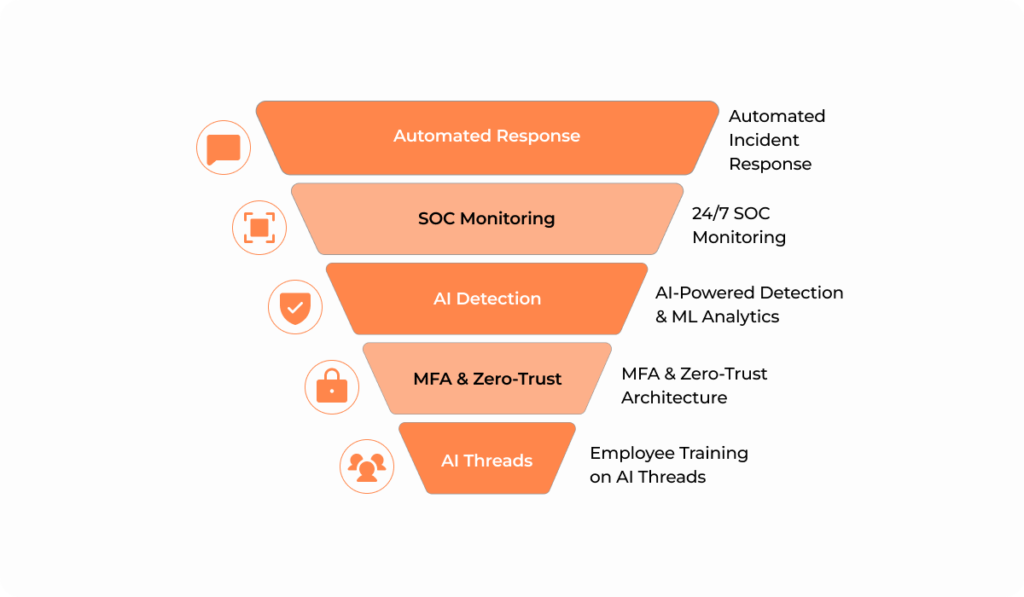
How We Help Protect Against AI Cybersecurity Threats
You don’t have to fight AI-powered cybersecurity threats alone. We make AI and cybersecurity work for you, not against you.
AI-Powered Cybersecurity Solutions: We implement advanced machine learning in cybersecurity tools that detect and neutralize threats in real-time. Our AI-powered cybersecurity platform adapts to new AI cybersecurity threats automatically.
Deepfake Phishing Prevention: Specialized training and technical controls help your team recognize and respond to deepfake phishing attempts. We implement verification protocols that stop social engineering attacks before damage occurs.
Proactive Threat Monitoring Using ML in Cyber Security: Our 24/7 SOC uses machine learning analytics to monitor your environment continuously. We catch AI and cybersecurity threats before they cause damage—not after.
AI-Specific Policy and Training: We build comprehensive policies addressing the use of AI in cybersecurity and train your staff to spot AI-powered attack warning signs. Awareness is your first line of defense against AI cybersecurity threats.
Vendor and Third-Party Vetting: We review third-party AI tools for security vulnerabilities and ensure they don’t introduce AI cybersecurity threats to your environment. Your partners shouldn’t become your weakest link.
Incident Response Planning for AI Attacks: When an AI-powered attack happens, every minute counts. We create detailed response plans specifically for deepfake phishing, AI cybersecurity threats, and ML in cybersecurity attack scenarios.
Netherlands-Specific Compliance Support: We understand GDPR, NIS2 Directive requirements, and how AI and cybersecurity regulations apply to Dutch businesses. Our solutions keep you compliant while keeping you secure.
The Future of AI and Cybersecurity
AI cybersecurity threats will only grow more sophisticated. As machine learning in cyber security attack development advances, the gap between protected and vulnerable businesses will widen.
Emerging AI-powered cybersecurity threats to watch:
✓ Quantum computing implications for encryption
✓ AI-powered supply chain attacks
✓ Advanced deepfake phishing using real-time video manipulation
✓ Autonomous AI and cybersecurity attack systems that adapt without human guidance
The organizations that survive aren’t those with the biggest IT budgets—they’re those that understand AI-powered cybersecurity defense and implement it strategically.
The use of AI in cybersecurity defense isn’t optional anymore. It’s the baseline for survival in a threat landscape dominated by machine learning and automation.
Don’t Wait Until It’s Too Late
Every day you wait is a day AI cybersecurity threats evolve. AI-powered attacks become more sophisticated, deepfake phishing becomes more convincing, and the use of AI in cybersecurity attacks becomes more widespread.
The question isn’t whether you’ll face an AI and cybersecurity threat. It’s whether you’ll be ready when it arrives.
Here’s what you need to do now:
✓ Assess your current security posture against AI-powered cybersecurity threats
✓ Implement multi-factor authentication to counter deepfake phishing
✓ Train your team on AI cybersecurity threats awareness
✓ Deploy ML in cybersecurity detection tools
✓ Establish verification protocols for financial transactions
✓ Consider managed AI-powered cybersecurity services if you lack in-house expertise
Let’s secure your business before AI-powered attacks strike.
We offer free security assessments for Dutch SMBs to identify vulnerabilities in your current defenses against AI and cybersecurity threats. No obligations, no sales pressure—just actionable insights to protect your business from deepfake phishing and other AI cybersecurity threats.
Or contact us at +31 203034260 / Helpdesk@cloudconnected.nl to discuss how AI-powered cybersecurity solutions can protect your specific business. Our Dutch-speaking security experts understand machine learning in cybersecurity and are ready to help.



